What Is GNSS Spoofing and How Is It Different from Jamming?
GNSS spoofing is a sophisticated attack where a malicious transmitter broadcasts counterfeit satellite signals, tricking a GNSS receiver into calculating a false position, velocity, or time. Unlike jamming, which simply drowns out legitimate signals with noise, spoofing deceives—the receiver believes it is somewhere it is not, or that the time is different from reality.
The difference is critical. Jamming announces itself: the receiver loses lock and reports “no fix.” Spoofing operates covertly—the receiver continues reporting a position, but that position is wrong. For UAV operations, jamming grounds the drone (annoying but safe); spoofing can redirect it to a hostile location, trigger a fly-away, or feed false telemetry to the operator. This makes spoofing far more dangerous for autonomous systems.
In practical terms, spoofing requires more equipment and technical knowledge than jamming, but low-cost software-defined radios (SDRs) have dramatically lowered the barrier. Attackers can now build a credible spoofing setup for under $500, making this a threat every GNSS-dependent operation must address.
Why Is GNSS Spoofing a Growing Threat in 2026?
The threat landscape in 2026 is grim. GNSS spoofing incidents have escalated across maritime, military, and civilian domains. In the Black Sea, ships have reported GPS showing positions at an inland airport—a mass spoofing event. Military conflicts in Ukraine and the Middle East have seen drone navigation systems systematically targeted with spoofing attacks designed to capture or crash UAVs.
The democratization of software-defined radio is a major driver. Open-source tools like GNU Radio, combined with HackRF or BladeRF hardware costing a few hundred dollars, enable attackers to generate convincing counterfeit GNSS signals. Online tutorials and forums share detailed methodologies. The barrier to entry has collapsed.
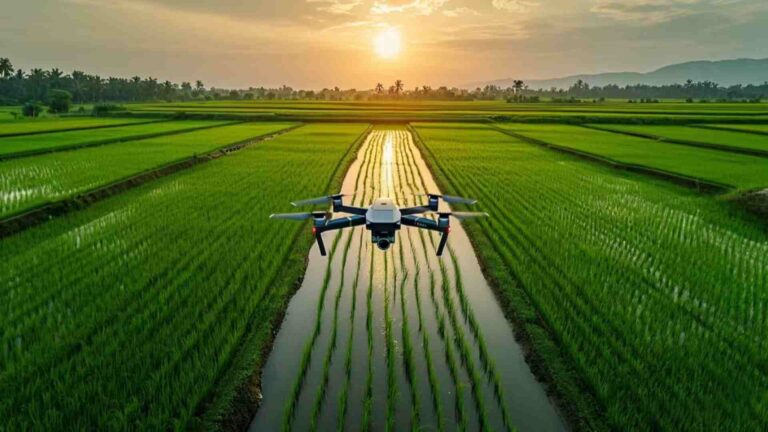
Commercial drone operators, surveyors, and agricultural users are increasingly reporting suspicious GNSS behavior—sudden position jumps, incorrect altitude readings, or inexplicable route deviations. Without anti-spoofing GNSS technology, these operations are flying blind, trusting signals that may be manipulated.
How Does Septentrio AIM+ Detect GNSS Spoofing?
Septentrio’s AIM+ (Advanced Interference Mitigation+) is a multi-layered defense system that protects GNSS receivers from both jamming and spoofing. Unlike basic interference filters, AIM+ is specifically designed to detect the subtle signatures of spoofing attacks.
First, AIM+ performs continuous signal monitoring. It analyzes signal power levels, carrier-to-noise ratios, and Doppler shifts across all visible satellites. A sudden cluster of signals with identical power profiles or suspicious Doppler patterns triggers the spoofing detection engine. Genuine GNSS signals from different satellites naturally arrive at slightly different power levels and angles—counterfeit signals tend to be unnaturally uniform.
Second, AIM+ runs consistency checks across multiple constellations (GPS, GLONASS, Galileo, BeiDou). A spoofer typically targets only GPS frequencies. AIM+ cross-references all constellations; if GPS says “here” but Galileo says “there,” the system flags the discrepancy. This multi-constellation approach makes spoofing exponentially harder because the attacker must simultaneously fake all GNSS systems.
Third, AIM+ integrates with Galileo OSNMA (Open Service Navigation Message Authentication), the free signal authentication service from the European Union. OSNMA cryptographically signs the Galileo navigation message, allowing the receiver to verify that the signal genuinely originated from a Galileo satellite. AIM+ receivers check this signature on every message. For more details, see our deep dive on AIM+ anti-spoofing technology.
Can Anti-Spoofing GNSS Technology Protect Military UAVs?
Yes—and it is increasingly essential. Military UAVs are prime spoofing targets. Tactical drones performing reconnaissance, surveillance, or precision strike missions rely entirely on GNSS for navigation. A successful spoofing attack against a military UAV could cause mission failure, loss of the aircraft, or—worst case—redirect the drone into friendly forces or civilian infrastructure.
Anti-spoofing GNSS technology for defense applications must go beyond basic detection. Military-grade requirements include: authenticated signals that cannot be cloned (OSNMA or similar), multi-frequency receivers that detect attacks across L1/L2/L5 bands, and redundant secure PNT (Positioning, Navigation, Timing) architectures that combine GNSS with inertial navigation systems (INS) and other sensors.
The approach we recommend for tactical UAVs pairs a spoofing-resilient GNSS receiver—like those powered by Septentrio’s AIM+—with an IMU for inertial dead-reckoning. If the receiver detects a spoofing attack, it can seamlessly transition to INS-only mode, maintaining navigational integrity even under active electronic warfare conditions.
What Is Galileo OSNMA and Does AIM+ Support It?
Galileo OSNMA (Open Service Navigation Message Authentication) is a free, publicly available service from the European GNSS agency that provides cryptographic authentication of Galileo’s navigation signals. It works by embedding a digital signature—the “navigation message authentication”—into the Galileo E1-B signal. The receiver validates this signature against a public key, confirming the signal originated from a genuine Galileo satellite and has not been tampered with.
OSNMA does not encrypt the signal (it remains free and open), but it adds a verification step that any spoofed signal cannot pass. A counterfeit signal cannot reproduce the correct cryptographic signature without access to the Galileo ground segment’s private key, which is physically secured.
Yes, Septentrio AIM+ fully supports Galileo OSNMA. Receiver firmware that includes AIM+ automatically performs OSNMA authentication on every Galileo message it receives. This means whenever Galileo signals are available (which is everywhere outside polar extremes), the receiver has a cryptographically guaranteed anchor of truth. Combined with the constellation cross-checks described earlier, OSNMA makes AIM+-equipped GNSS receivers among the most spoofing-resilient units available at any price point.
How to Choose a GNSS Receiver with Anti-Spoofing Protection?
When evaluating GNSS receivers with anti-spoofing protection, consider these criteria:
- OSNMA support — Non-negotiable for 2026. If the receiver cannot authenticate Galileo signals, it is vulnerable to spoofing.
- Multi-constellation, multi-frequency — Receivers that track GPS L1/L5, Galileo E1/E5a, GLONASS L1/L2, and BeiDou B1I/B2I simultaneously have far more data to cross-check for anomalies.
- AIM+ or equivalent interference mitigation — Dedicated anti-spoofing algorithms, not just basic interference filters.
- Firmware update path — Spoofing techniques evolve. Choose hardware with active firmware support.
Our top recommendations:
- HB21 GNSS Box Receiver — All-in-one RTK receiver with 4G LTE, heading, and data logging. Powered by Septentrio mosaic-H (AIM+ enabled).
- HB6 GNSS Box Receiver — Compact quad-constellation RTK receiver with full AIM+ spoofing protection.
- EV322 GNSS Receiver — Lightweight RTK receiver purpose-built for UAVs, with AIM+ anti-spoofing.
How Does AIM+ Secure PNT for Defense Applications?
PNT—Positioning, Navigation, and Timing—is the foundation of modern defense operations. Military vehicles, aircraft, ships, and soldiers all depend on accurate, trustworthy PNT data. When spoofing attacks compromise PNT, the consequences range from mission degradation (wrong coordinates) to catastrophic failure (friendly fire, navigation into hostile territory).
AIM+ secures PNT through its three-layer defense: detection (identify the attack), alert (notify the system or operator), and mitigation (maintain navigation through alternative PNT sources or INS fallback). For defense applications, it is the mitigation layer that truly matters—the ability to continue operating under attack.
By authenticating Galileo signals via OSNMA, cross-checking all constellations, and feeding clean position data to the mission computer, AIM+ provides the assured PNT that defense users require. This transforms GNSS from a single point of failure into a hardened, resilient component of the navigation architecture.
Ready to Protect Your Operations from GNSS Spoofing?
GNSS spoofing is not a theoretical risk—it is a present-day threat. Whether you operate UAVs for surveying, agriculture, defense, or logistics, the question is not if you will encounter spoofing, but when. Protect your operations with receivers that combine Septentrio’s AIM+ technology, Galileo OSNMA, and multi-constellation tracking.
Browse our range of GNSS receivers with anti-spoofing protection or contact our team for a consultation on your specific operational requirements.
FAQ
What is the difference between GNSS jamming and spoofing?
Jamming overwhelms the GNSS receiver with noise, causing loss of signal. Spoofing transmits counterfeit signals that deceive the receiver into calculating a false position. Jamming is a denial-of-service attack; spoofing is a deception attack. Spoofing is far more dangerous because the operator may not realize the system has been compromised.
Can consumer-grade GNSS receivers detect spoofing?
Most consumer-grade receivers have no spoofing detection. They trust whatever signals they receive. Detection requires specific anti-spoofing technology like Septentrio AIM+ or support for Galileo OSNMA. Without these, a consumer receiver will happily output fake positions from a spoofing attack.
Is OSNMA really free?
Yes. Galileo OSNMA is a free, open service from the European Union. Any GNSS receiver manufacturer can implement OSNMA support in their firmware at no licensing cost. The only cost is the firmware development effort. As of 2026, most Septentrio-based receivers (including our HB21, HB6, and EV322) ship with OSNMA support enabled.
What should I do if I suspect active spoofing?
If your GNSS receiver alerts to a spoofing attack: (1) Do not trust the displayed position. (2) Switch to inertial or visual navigation if available. (3) Land the UAV immediately if the spoofing confidence is high. (4) Log all receiver data for post-incident analysis. AIM+-equipped receivers will automatically flag spoofing events with confidence levels.
Related GNSS Products
- HB21 GNSS Box Receiver — All-in-one RTK receiver with 4G LTE, heading, and data logging.
- HB6 GNSS Box Receiver — Compact quad-constellation RTK receiver.
- EV322 GNSS Receiver — Lightweight RTK receiver for UAVs.
- AIM+ Anti-Jamming & Anti-Spoofing Technology — Military-grade protection.
About the Author: Jack is a GNSS integration specialist with over 6 years of experience in UAV navigation systems, working with Septentrio receivers, RTK positioning, and ArduPilot/PX4 flight controllers.